 As many of you who are subscribed to my Facebook and Twitter accounts will know, Leaving Work Behind was hacked a couple of weeks ago.
As many of you who are subscribed to my Facebook and Twitter accounts will know, Leaving Work Behind was hacked a couple of weeks ago.
For two days the site was either complete offline or in a rather mangled state. For two days my hosting provider and I worked our asses off to get LWB back online. It was an experience that I would rather not go through again, and one that I hope you will never have to go through.
With that in mind, in this post I want to outline the comprehensive steps I have taken to make my site more secure. I have spoken to some of the most influential and respected web security guys out there over the past couple of weeks and have been able to distill their wisdom into this post. It is my hope that you will take action on these steps to make your WordPress website(s) far more secure.
Why Websites Get Hacked
A lot of people seem to have it in their heads that hackers are mastermind plotters who manually seek out weak websites in an evil and calculated fashion (or something along those lines). While I’m certainly not one to defend hackers, that image is rather false in the vast majority of cases.
Sure — you do have hackers who will target a specific high-profile site for political reasons and so on, but unless you’re a BBC.co.uk or a Mashable you probably don’t need to worry about that. With the greatest of respect, your site probably isn’t big enough to be worth a hacker’s specific attention.
At the small/medium site level, hackers are generally looking to do one of two things:
- Use your website as a means of building a botnet of servers which they can use to do bigger and badder things
- Infect your website with malware that will drive search engine traffic etc. elsewhere
While there are some hackers out there who will hack sites just for the hell of it, they more often than not have an agenda. For instance, many hacked sites have their SEO meta data altered so that search rankings look like advertisements for pharmaceuticals, for which hackers can earn a healthy commission.
How Websites Get Hacked
When us “normal” folk get hacked it is typically the result of just one thing: an automated program exploiting a security vulnerability.
These vulnerabilities can be widespread or individual to your blog. Arguably the most high profile WordPress security vulnerability in recent years was the TimThumb saga, in which an image-resizing library used within many premium themes was exploited to gain control of a site.
On the other hand, hackers can used automated botnets to scour the web in search of websites that are vulnerable to “brute force attacks“ — i.e. the login details are obvious enough to allow a hacker to gain entry by attempting numerous logins. Imagine having all the time in the world to crack a digit-dial safe and you get the idea.
In reality, the fear of hacking gets blown entirely out of proportion. There is no bogey man waiting around the corner with the malicious intent of destroying your pride and joy. There are just those who indiscriminately target the weak. Therefore, all you need to do is make your site strong.
How to Protect Your WordPress Website
WordPress security is one of those topics that can get seriously overwhelming. You’ll get hit with a huge number of tips and tricks that will supposedly make your site more secure, but in reality you have no idea as the efficacy of those measures.
With that in mind, I want to take a different approach here. I’m going to run through the ten most effective steps you can take to secure you site. By acting on just these ten steps, your site will be far more secure than the vast majority of others out there, and even if your site is hacked, you’ll be in a position to restore it quickly and with minimum fuss.
Step 1: Backup
 Let’s start with the single most important thing you should do to keep your site secure: take regular backups.
Let’s start with the single most important thing you should do to keep your site secure: take regular backups.
You must take this step first and make sure that you have a backup before you make any other changes to your site.
Nothing is more effective at securing your site than having backups. You can never make your site 100% secure — such a thing is not possible — but you can practically guarantee its safety by making sure that it is regularly backed up in a safe and reliable manner (and as such, can be restored).
In the past I have been rather lax with my backups process. I have taken backups but I’ve done it with a service that isn’t particularly reliable. In fact, I had to rely upon my hosting provider’s daily backup service to restore my site after it had been hacked.
Therefore, I knew that I had to upgrade to something bulletproof. After doing a fair bit of research I settled on VaultPress — made by Automattic, the same fine folks who help to develop WordPress. It takes a snapshot backup of my site every single hour and stores all of those backups in perpetuity:
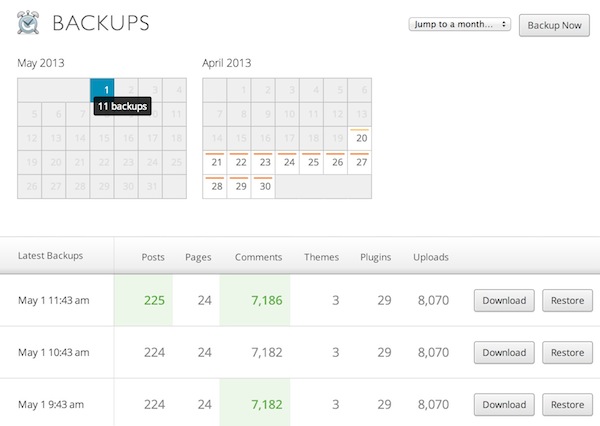
Not only that but VaultPress also offers a one-click site restore option, daily security scans, a comprehensive activity log, and more. All of this starts at just $5 per month (I’m subscribed to the premium $40 package).
I urge you to go with VaultPress. It’s not an affiliate link; I just think it’s a superb service.
Step 2: Update Everything
Okay, now let’s move onto some quick fixes that will dramatically improve the security of your site.
Rule 101 of site security is this: update everything regularly. I spoke to Dre Armeda, CEO and co-founder of Sucuri, and he highlighted it as the most important thing you can do to improve your site security (on any platform, not just WordPress).
And when I say update everything, I really mean everything:
- The WordPress Core
- All themes (including those that are deactivated)
- All plugins (including those that are deactivated)
WordPress has arguably the best team out there for spotting security vulnerabilities and patching them within a matter of days or even hours. All you need to do is keep up.
In an ideal world you would run updates as soon as they became available, but that may not be practical. I would recommend that you login once every day or two to run any pending updates.
Step 3: Clean House
An updated theme or plugin does not necessarily mean that it is safe. After all, you could have an “up-to-date” plugin that has in fact not been updated for two years.
So now’s the time to check over your themes and plugins and get rid of anything that is clearly no longer updated. As a rule of thumb I allow plugins that have been updated within the last year.
An easy way of spotting these plugins is to install Plugin Last Updated. This will show you the date upon which a plugin was last updated within the Plugins screen:

You should also get rid of any themes and plugins that you do not need. Whether active or otherwise, they still represent a potential security vulnerability and simply shouldn’t be there. The rule of thumb here is: if it’s not need for the site then it shouldn’t be on your site. It’s that simple.
Step 4: Manage Your Profiles
Head over to Users > All Users via your WordPress sidebar and you’ll be presented with a list of all active users on your site.
The first thing you should do is delete any redundant users. You can transfer the ownership of any posts written by that user to another user during the process.
Then downgrade any inappropriate roles for users. For instance, if you have contributors on your blog, they do not need Administrator access. Downgrade them to Author. This means that they will not have access to sensitive areas of your site’s backend.
Finally (and perhaps most importantly), get rid of your “admin” profile (if it’s still there). Many brute force attacks are based upon attempting to crack the password for “admin” accounts — if you change the name, you completely prevent the attack from being successful.
The easiest way to successfully delete your admin profile is to create a new Administrator profile, delete the old admin one and select the option to transfer all posts to the new profile. Please make sure that you have taken a backup before you attempt this!
Step 5: Change Passwords
When I say passwords, I mean all of them.
Now is the time to get your house in order and ensure that all of your accounts are safe from a brute force hacking attempt. Here is an incomplete list of the account passwords you should be changing:
- All WordPress profiles
- Your hosting account
- FTP
- Your email account
- Your social media accounts
- Your PayPal account
- Your Amazon account
You get the idea. Each password should be completely unique and used on only one site. And please do not use recognisable words in your passwords.
To create strong, unique and random passwords, I recommend that you use the LastPass Random Password Generator with the settings as follows:
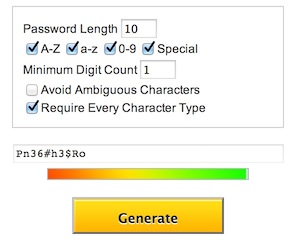
While you’re at it, get a free subscription to LastPass and use it to store all of those complicated passwords you’ve just created. Then you only have to remember one password to gain access to all of your accounts.
Step 6: Disable FTP (and Set Up SFTP)
Here’s something you may not know: FTP (File Transfer Protocol) is horribly insecure. In a nutshell, it transfers all files and data in an unencrypted format, which means that anyone who successfully intercepts it can see exactly what’s inside.
So get in touch with your hosting provider now and ask them to (1) disable FTP and (2) enable SFTP (SSH File Transfer Protocol). This is absolutely vital to the security of your site. After all, it doesn’t matter how secure your WordPress login is if hackers can get in via FTP. With FTP access they have everything they need to gain full control over your site.
Step 7: Consider Your Hosting Solution
 I love Westhost — the guys who host Leaving Work Behind and all of my other sites. My bond to them was only strengthened by the way in which they dealt with the hacking of my site.
I love Westhost — the guys who host Leaving Work Behind and all of my other sites. My bond to them was only strengthened by the way in which they dealt with the hacking of my site.
First of all, their automated ModSecurity firewall system detected the incursion and immediately took the site offline, probably saving it from being defaced even further. Secondly, they worked their socks off to get the site back online, even though they were busy with many other folks who were facing the same issue. Finally, it was their daily backups that we relied on to get the site back online.
In a way it’s timely that this hack occurred, as it was only a few weeks ago that I published a glowing endorsement of Westhost here on LWB. I am glad that my faith has been rewarded.
Obviously I would recommend Westhost for hosting your site, but whoever you choose to go with, I recommend the following features:
- ModSecurity
- SFTP support
- 24/7 local telephone support
- Daily backups (having a backup for your backups is never a bad idea)
I cannot underestimate the importance of your hosting provider for any number of reasons, so make your decision carefully.
Step 8: Consider Security Plugin Solutions
WordPress security plugins are all the rage these days, which is rather unsurprising given the high-profile security issues revealed in the press recently. But a little birdie (whose opinion you’d do well to trust) told me that their role in website security is often blown out of proportion. Although certain WordPress security solutions can be useful, it is the previous seven steps that will make the greatest difference.
Although there are countless options available, I would narrow the selection down to:
They’re all very popular and highly rated. I personally use Wordfence but you may wish to take the time to consider the two alternatives. Regardless of which one you choose, they implement a lot of measures that will make your site that little bit more difficult to hack.
Step 9: Subscribe to Sucuri
 Finally we have what I consider to be the finest website security scanning and cleanup service currently available.
Finally we have what I consider to be the finest website security scanning and cleanup service currently available.
In a nutshell, the aforementioned Sucuri regularly scans your website for malware and anything else untoward and takes instant action (with your permission) to restore your site to its intended glory within hours.
Like VaultPress it is another premium solution, but there is a reason for that — the service is top-notch. And let’s face it: $90 per annum (or $7.50 per month) is not a particularly big price to pay for a service that will constantly keep an eye on your site and restore it quickly if the worst should happen.
Step 10: Ensure that Your Computer is Secure
Finally, you should look closer to home to ensure that your site is safe from hackers.
Consider this: creating a highly unique password is potentially worth nothing if there is keylogger malware installed on your system. Therefore, you should strive to ensure that your computer is as secure as possible too.
The same principles covered above apply:
- Ensure that your OS and all software is regularly updated
- Delete anything that you don’t need
- Create strong, unique passwords
In addition, make sure that strong firewalls are set up between your computer and that you have a top-notch antivirus solution in place. Do not rest until you feel that your computer is as secure as it can be!
There is No Such Thing as 100% Secure
I am sure that some of you will have additional suggestions to boost website security and I welcome them in the comments section.
However, bear this in mind: there is no such thing as a 100% secure site. You could go on and on practically forever in an effort to improve the security of your website, but ultimately there comes a point where you decide that it is safe enough.
I believe that the ten step process I have outlined above will ensure your website’s safety against the vast majority of attacks, and perhaps most importantly, the high-profile attacks that you are probably worried about. WordPress security isn’t particularly complicated when you boil it down to the absolute fundamentals, which are all covered above.
If you have any questions or comments then please do not hesitate to fire away in the comments section below!
Hi Tom,
Sorry to hear that your site was hacked, but good to see that it’s right back where it belongs! A few more easy-to-implement suggestions –
(1) One should never use “admin” for an administrator account username
(2) The publicly displayed name and the username shouldn’t be the same
(3) Use a plugin such as Login Lockdown or Limit Login Attempts (both are free)
Now I better go and make some of the changes you’ve suggested to my site!
Hi Reeta,
All good suggestions — I’m going to add the “admin” one to the post itself. I should mention that the functionality of Login Lockdown, etc is included within those plugin options I listed 🙂
Cheers,
Tom
I actually do not understand most of what you are saying. I know #10, keeping my computer secure. But, why would I want to subscribe to sucuri (#9), and WordPress as a host? That doesn’t make any sense to me. I guess I don’t understand the difference there. Also, as to #1, where am I supposed to back up my wordpress blog??? As to #2, how am I supposed to ‘update’ wordpress’ core, themes…And #3 what is this about plugins? How am I supposed to update a plugin from a static, free, blog site? #4 and 5 actually make sense (in the “I understand what you are saying” way). #6 I surely have no idea about, especially since wordpress is free. I have already admitted to complete bafflement of what you are saying on #8, and 9. I have already addressed #10. I sure would like to be more ‘secure’ but I really don’t get what you are saying here. It sounds like a lot of ads for duplicate products??? Clarity, please.
You’ve probably got WordPress.com and a self-hosted WordPress confused. If you’re on .com there are no Plugins or Updates.
And if you’re on .com you have no need for FTP (File Transfer Protocol) programs to upload content to your blog. You can use your dashboard for that.
The hosting, well that’s covered with a .com install. If not, it’s recommended you select your hosting on said requirements.
Sucuri just scans your website for any malware and gives you the oppurtunity to remove that malware.
Hope that clarifies it a bit?
Hi Sande,
Apologies for not offering the clarity you require. It sounds like you’re using WordPress.com, not self-hosted WordPress. This post applies to self-hosted WordPress. I only recommend two premium products in the entire post and only one of them is an affiliate link, so I can assure that there aren’t “a lot of ads for duplicate products.”
Cheers,
Tom
Nice article. There’s probably going to be a ton of comments with extra security measures, but there’s one a lot of people seem to forget:
Check your wp-config.php and see if the Authentication unique Keys and Salts are filled out. If not, use the secret key generator (link is in the wp-config).
Lot of automated WordPress installs neglect this part, so it’s worth checking out and will only take you a second!
Good one Niels although perhaps a little confusing for those of us not used to diving into the PHP files that make up WordPress. Definitely something that you should look into if you’re feeling adventurous 😉
While I’m the first person to suggest everyone perform updates religiously (it’s actually one leg of my business), updates alone are insufficient for ensuring that you’re not infecting your site.
For example, just this last month one of the very popular plugins (almost a million downloads) was infected and was still being published through the WP repository. Likewise, a couple years ago there were several plugins that were simultaneously infected – again, some very popular stuff – and continued to be promoted and distributed through the WP repository. That incident spawned changes within the WP distribution system, but as the Social Media Widget fiasco of last month demonstrates, human and automated testing for malware is limited, and sometimes a little patience is more important than blindly installing every update.
There’s even a common method of exploiting third-party plugins and themes by harvesting their installation base via the WP repository, so assuming that a privately written or a third-party ‘professional’ version of a plugin is going to be safe is folly as well.
Another thing people should be aware of is that a “security plugin” is *not* a panacea. In fact, all three of the “security plugins” you listed have historically included exploitable code:
* Better WP Security
* BulletProof Security
* Wordfence Security
Again – having a host or developer that knows this stuff is more important than a plugin that could actually make things worse.
Updates are absolutely essential – but users that are not familiar with the underlying mechanisms or aren’t willing to learn should find an experienced third party to help them manage this type of thing.
Hey Shawn,
I hope you felt I made it clear in my post that I don’t think the aforementioned plugins are a panacea — that certainly wasn’t what I was going for.
As for the malware, that’s exactly why I’d recommend a subscription to Sucuri. The link you provided was in fact to the Sucuri blog and I know that they jumped on that issue for subsribers’ blogs.
Security is no joke but I don’t think you need help from an “expert” to be relatively safe — I think the steps above are pretty comprehensive.
Cheers,
Tom
WordPress is much more vulnerable to hacking than blogger, but at the same time blogger is only for casual and part time bloggers. I wanna migrate to WordPress but this these frequent incidents are making me thing twice. It’s really a dilemma.
The benefits of using blogger isn’t the platform so much as the responsibility – Google is responsible for maintaining the servers, security and so on. It’s essentially a closed platform. That’s great from a security standpoint – but only as long as you trust Google. For example, Google has a habit of buying out major web projects or spending years investing and developing them, and then simply turning them off. Here’s a few they’ve done this to: Google Reader, Google Sync, Google Wave, Vark, Meebo, CalDAV, Google Cloud Connect, Google Voice for Blackberry, Search API for Shopping, Google Apps for Teams, Youtube Groups, iGoogle, Product Search, City Tours, Google Mini, Google Page Creator, Google Desktop, Google Gears, and dozens more.
While you might not have to worry about maintaining your own server or site as others do today, when they decide that BlogSpot/Blogger is no longer a valuable investment (it will probably be announced next March), your site and everything on it will be lost. Sure, they provide nifty tools to get your data before they turn your stuff off, but they *will* eventually turn it off, and all the efforts you’ve put into developing it and learning the platform will be a drop in the bucket.
WordPress has two variants: .com and .org. The .com version is similar to Blogger/BlogSpot: it’s a hosted solution that you don’t have to worry about the management aspect of your site. That’s nifty, but the real power behind wordpress is in .org. With this version of wordpress you can install it on your own site, hosted anywhere, and you can control all the code with advanced plugins, themes and have access to the source for all of it. You have absolute control.
“With great power comes great responsibility” – and if you’re going to do this, you need to maintain it (or hire someone to maintain it). There’s simply no other way to ensure that Joe’s honest coding mistake yesterday isn’t going to be tomorrows worldwide hosting catastrophe.
At the very least, if you’re using Blogspot/Blogger today, get your own domain name immediately and use that as your primary address. I discuss this issue in more detail here.
Thanks for the heads up Shawn. I seriously never considered that they could shut down their blogger service in a blink. I have already purchased the domain from GoDaddy. Now all I need to do is select a good hosting plan and move on to WordPress for more serious blogging.
Hi Rahul,
What makes you think that WordPress is more vulnerable than Blogger? I would highly recommend migrating — WordPress is as safe as any CMS out there if you take reasonable precautions.
Cheers,
Tom
If I move on to WordPress, will my posts, comments and backlinks be effected. If yes, then to what extent?
You can migrate all your content (the blogger importer does a pretty good job, but not great).
Unfortunately, if you’ve been using a blogspot URL (not your own domain) then you’re pretty much screwed with the backlinks. You’ll need to contact each of the webmasters of sites linking to you to correct the links. There’s simply no other reliable way to fix it.
Hey Tom – glad that you’re back up and running! I’ve forwarded your post to our web developer so that he can implement some of these steps with our clients. You can never be too secure :-).
Thanks Ruth!
Hey Tom,
This is my very exhaustive and detailed list. I like the way you covered it in so much detail. It actually surprises me how many people take this advice as an afterthought, yet spend hours crafting their posts and updating their blog. All the hard work can be wiped out in an instant if you haven’t been following ‘best practices’ and ensuring your passwords are secure. I have to say, I haven’t tried that password manager yet. I’ve used PassPack. Are they similar? Which one do you think is better?
Hi Rob,
I’m not familiar with PassPack so I can’t pass judgment, but I do really like LastPass.
Cheers!
Tom
Hi Rob,
I’m not familiar with PassPack so I can’t pass judgment, but I do really like LastPass.
Cheers!
Tom
Tom!
You are my hero! Thank you so much for taking the time to tell your story to try and help us avoid the same misfortune.
Awesome resource and great site.
Susi
Thanks Susi, very kind of you to say so 🙂
Thanks Tom for a concise and well written post!
Pleasure Chris 🙂
Great Post Tom!
I’d also suggest putting your site behind a firewall as well. A CDN can also help. I found Cloudflare.com to be the easiest and cheapest way to go. I suffered a denial of service attack and cloudflare took care of everything by simply switching IP’s i had only 1 hour of downtime, they also optimize your site for you and takes 5 seconds to implement. Leaving Work Behind would definitely benefit from this! Best of all if your site does go down the CDN has your pages cached and visitors can still access parts of your site even if the server is turned off.
Hi Chris,
Unless I am mistaken, the ModSecurity system I recommend about is a firewall.
I’ve heard a lot of good things about CloudFlare…may have to check them out in more detail. Thanks!
Cheers,
Tom
Good to know about not using ‘admin’ as a security measure. I’m going to have to do that.
While it’s important to change the ‘admin’ username, you should also add the following to your htaccess file, otherwise any attacker that wanted to discover your username simply needs to visit “/?author=1”:
RewriteEngine On
RewriteBase /
RewriteCond %{QUERY_STRING} (author|path|tag)\=\.?/? [NC]
RewriteRule .* – [F]
Put it ABOVE the WP stuff in your .htaccess file.
The comment system clipped out the ‘ifmodule’ stuff before and after, so make sure you add those in, too.
That’s a definite!
Hey Tom, I was surprised to see that you didn’t recommend ManageWP for both site backups and security screening, since you write their blog. I recently signed up for that service after a lot of deliberation between ManageWP and Vaultpress. Now I’m hoping that it was ManageWP that you referred to as not being particularly reliable? Thank you!
Hey Elliott,
No, certainly not! In my opinion VaultPress and ManageWP are too very different services with a slight overlap in functionality. ManageWP’s backup service is great but only backs up once per day — I want something more regular than that. Plus ManageWP uses Sucuri for screening, so that’s actually inbuilt into my recommendation 🙂
Cheers,
Tom
Great to hear that, thanks. I think I can manage on one backup a day for now, so ManageWP it is. I know that they also provide a lot of other services in maintaining websites, but I actually signed up primarily for the backups and security.
Hey Tom.
So far, I’ve read four articles from you and have decided to follow you more closely, as your posts are thoughtful and pragmatic. That being said, I’m a bit confused about the security plugins you’re recommending. In one post you sang the praises of WordFence (as you have done here). In a second one devoted to Security Ninja, you indicated that this plugin was a must since it provided very strong malware scanning & protective advice if malware is discovered, as well as firewall protection, along with some of its other features.
In this post you added two other plugins that are not only very popular but are highly rated in the WordPress community, these being Better WP Security and BulletProof Security.
Now apart from doing all of the other steps, how would you recommend I narrow down (if at all) these four plugins that are strong contenders but also do different subsets of security (as well as having some overlaps).
I’m a complete technophobe and a newb when it comes to WordPress and was wondering should I go with 2, 3 or all four installed, and if 2 or 3, which ones should those be? Would really appreciate hearing your insights on this subject. Thanks for the extremely valuable advice, by the way!
Hi Larry,
For automated security my recommendation is Wordfence. I included the other two popular plugins in the interests of full disclosure.
Security Ninja isn’t so much a malware scanner as a security vulnerability scanner. You can use it to find historically exploited security holes in your WP installation that you can then shore up. It complements rather than replaces Wordfence and the like.
Here’s the thing: if you take all of the other security steps then installing a plugin like Wordfence is probably overkill (but welcome overkill, nonetheless). I’d advise that you follow all the other steps and install Wordfence for step 8.
Cheers,
Tom
Thank you so much for doing this awesome post Tom.
So much solid information here.
With all the recent scares related to wordpress this was a very timely post for many people I imagine.
No problem Iain! You may like this too: https://managewp.com/is-wordpress-secure
I read that one actually. It was also a very sweet post.
You’re doing great over there at ManageWP
Thanks Ian!
Tom,
Almost every day I get an email where someone tried to log in to my site using “admin” and got locked out. Whenever this happens, I think of you. I’m sorry your site was hacked, but I’m also grateful because your experience made it real for us. Thanks!
My pleasure Chris — it’s all in the past now (hopefully permanently!).
Hi Tom, thanks for a fantastic article. I am confused about backups as a security measure. While understanding the value of a clean, reliable backup from which you can restore your site, what happens if your site becomes infected without you knowing about it before you back it up. Wouldn’t you then just accumulate a number of faulty backups that would be useless to restore from? Many thanks again for the great information and advice.
Possibly, which is why it would be sensible to subscriber to Sucuri 🙂
fabulous article! quite sorry about your hack, and so happy that it resulted in a great comprehensive article with information for the rest of us.
thank you 🙂
Pleasure Sandy 🙂
Hi Tom, thanks for such a wonderful article. Security is one aspect everyone should take is seriously when it comes to managing user information and critical data on your site.
I have started to build my own site and your article has saved me a lot of time. I recently installed another plugin called “Stop Spammers” which really helps to cut down a lot of fake registrations.
Thanks again for the fantastic article 🙂
My pleasure Ravi 🙂
Tom, thanks for taking the time to hit this one out of the park. I’ve been reading on WP security for a few days now and this article answered all my questions. A lot of people are not looking at security until it’s too late. Guilty myself. It’s a growing concern and you have to be prepared. The more I read on it, the more I realize that everyone needs to migrate in the direction of a secure website. Very informative resources. Glad your back up, and many thanks!! Best wishes.
Cheers Richard!
Dear Tom,
Thanks for these helpful advices. WordPress indeed is a very friendly for content editors, but vulnerable to malware and hackers.
If the website’s market is national then you may ask the server at least to block access to it from abroad, but if the website’s market is worldwide, then your suggestions would be the only solution.
Best,
Roei